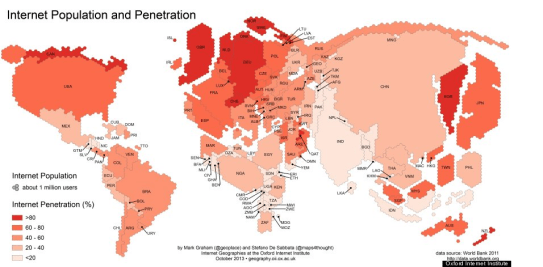
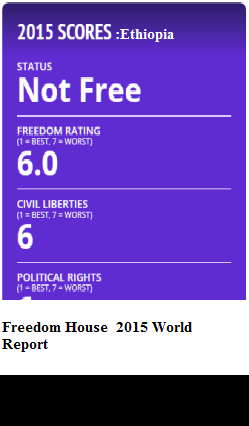
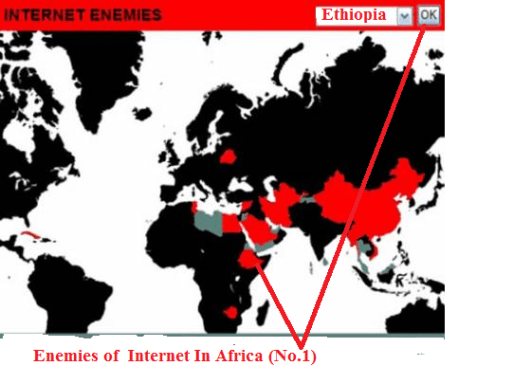
ETHIOPIA, The Gambia and Sudan are some of the most repressive places in Africa for online freedom, a new report by watchdog organisation Freedom House indicates, while South Africa and Kenya are the among the most free for internet users in the continent.
But the 12 African countries surveyed show a worrying trend – the majority are becoming more repressive compared to last year. Just South Africa – the best ranked – Kenya, Uganda and Malawi have maintained the same score as last year; Nigeria, Angola, Rwanda, Zimbabwe, Sudan and Ethiopia have deteriorated. Zambia and The Gambia are new entrants on the list this year.
The negative trajectory in internet freedom is mirrored around the world – the report states that in 36 of the 65 countries surveyed, internet freedom scores have become worse, as governments become increasingly nervous about their national security, and more sophisticated in surveillance and control.
“Very few countries registered any gains in internet freedom, and the improvements that were recorded largely reflected less vigorous application of existing internet controls compared with the previous year, rather than genuinely new and positive steps taken [by governments],” the report states.
Although most African countries do not explicitly censor content much, there has been an increasingly harsh manner in which users are targeted for the things they say online – in some countries, Freedom House reports, “the penalties for online expression are worse than those for similar actions offline”.

A higher score means a more repressive environment. Source: Freedom House
In July 2013, for example, the Gambian government passed amendments to the Information and Communication Act that specifically criminalised the use of the internet to criticise, impersonate, or spread false news about public officials. Anyone found guilty could face up to 15 years in prison, fines of roughly $100,000, or both—significantly harsher punishments than what the criminal code prescribes for the equivalent offenses offline.
The report reveals that breaches in cybersecurity are also eroding freedom, as government critics and human rights organisations are subject to increasingly sophisticated and personalised malware attacks, documented in 32 of the 65 countries examined.
Low internet penetration, state monopoly
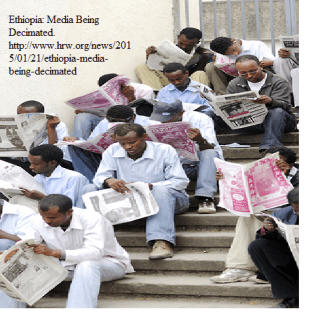
Ethiopia comes out as the worst place in Africa for internet freedom. In the first place, lack of telecoms infrastructure, government monopoly and oppressive regulation means that internet penetration is just 2%, one of the lowest in Africa.
A law enacted in November 2013 gives the Information Network Security Agency (INSA) carte blanche to inspect private online activities without oversight. Facebook, Twitter, Yahoo, and CNN were inaccessible for 12 hours in July 2013, while the number of permanently blocked webpages also increased.
In the Gambia, as well as setting out punitive new laws, internet cafe registration regulations were tightened in September 2013, requiring operators to provide thorough details for a license, as well as mandating the physical layout of cafes and the signs that must be displayed.
In Nigeria too, cybercafés have to keep a log of their customers – although the mobile revolution means that these attempts at controlling internet use will become increasingly irrelevant.
But if you can’t control access, then persecution and punishment becomes the next measure – and African governments show remarkable sophistication here.
In Ethiopia, the government launched high-tech surveillance malware against several online journalists in the Ethiopian diaspora and dissidents in exile; six bloggers of the prominent Zone9 blogging collective were arrested in April 2014 on charges of terrorism.

This year shows a more repressive environment than last year in many countries. Source: Freedom House
The same was observed in Angola, where “insider sources” affirmed that a German company had assisted the Angolan military intelligence in installing a sophisticated communications monitoring system on a military base, the report states. Further evidence, as of November 2013, found that at least one major ISP hosts a spyware system directly on its server.
In Rwanda, a growing number of independent online news outlets and opposition blogs were intermittently inaccessible in Rwanda in the past year. The Law Relating to the Interception of Communications enacted in October authorised high-ranking security officials to monitor email and telephone conversations of individuals considered potential threats to “public security”.
In Sudan, a localised internet service disruption in June and a nationwide blackout in September corresponded with large anti-government protests; the blackouts were reportedly directed by the government.
Even in the countries ranked as relatively free, harassment and intimidation of journalists and bloggers – and even ordinary citizens – is a widespread form of internet control. In Malawi online journalists are “periodically detained and prosecuted for articles posted on news websites”.
Most recently, Justice Mponda, a correspondent for the online publication Malawi Voice, was arrested in November 2013 for allegedly “intimidating the royal family” in an investigative story about former President Banda’s connection to the theft of millions of Malawian kwacha from government coffers in a scandal known as “Cashgate.” He was later acquitted.
Mugabe’s digital ‘death’
But it’s Zimbabwe that has had some of the most bizarre persecutions. An editor at the Sunday Mail state newspaper, Edmund Kudakwashe Kudzayi, was arrested in June on accusations of running the Baba Jukwa Facebook account, an activist page of over half a million followers harshly critical of the government. In July, the government took down the facebook page, and Kudzayi’s case remains unresolved.
It gets crazier – in January 2014, teenage Facebook user Gumisai Manduwa was arrested for allegedly insulting the president after he posted on his Facebook page that President Mugabe “had died and was being preserved in a freezer.” Manduwa was released on bail two days after his arrest. His case remains on the court’s docket as of mid-2014.
And another court case, this one against 21-year old Shantel Rusike is still being dragged through the magistrate courts in Bulawayo as of mid-2014.
Rusike was arrested on December 24, 2012 and held for four days after she was reported to the police for sending an image depicting President Mugabe “in a nude state” via WhatsApp on her mobile phone. Rusike faces charges of “causing hatred, contempt or ridicule of the president”.
Ethiopia
2013 2014
Internet Freedom Status Not Free Not Free
Obstacles to Access (0-25) 22 23
Limits on Content (0-35) 28 28
Violations of User Rights (0-40) 29 29
TOTAL* (0-100) 79 80
* 0=most free, 100=least free
Population: 89.2 million
Internet Penetration 2013: 2 percent
Social Media/ICT Apps Blocked: Yes
Political/Social Content Blocked: Yes
Bloggers/ICT Users Arrested: Yes
Press Freedom 2014 Status: Not Free
Key Developments: May 2013 – May 2014
• Telecom services worsened, characterized by frequently dropped phone calls, prolonged internet service interruptions, and slow response times to service failures (see Obstacles to Access).
• Facebook, Twitter, Yahoo, and CNN were inaccessible for 12 hours in July 2013, while the
number of permanently blocked webpages also increased (see Limits on Content).
• A law enacted in November 2013 gives the Information Network Security Agency (INSA)
carte blanche to inspect private online activities without oversight (see Violations of User
Rights).
• The government launched sophisticated surveillance malware against several online journalists
in the Ethiopian diaspora and dissidents in exile (see Violations of User Rights).
• Six bloggers of the prominent Zone9 blogging collective were arrested in April 2014 on
charges of terrorism (see Violations of User Rights).
Introduction
Ethiopia continues to have one of the lowest rates of internet and mobile phone connectivity in the world, as meager infrastructure, government monopoly over the telecommunications sector, and obstructive telecom policies have significantly hindered the growth of information and communication technologies (ICTs) in the country. Coupled with highly repressive laws and tactics aimed at restricting freedom of expression and access to information, internet freedom in Ethiopia is consistently rated the worst in sub-Saharan Africa and among the worst in the world.
Despite the country’s extremely poor telecommunications services and a largely disconnected population, Ethiopia is also known as one of the first African countries to censor the internet, beginning in 2006 with opposition blogs.1. Since then, internet censorship has become pervasive and systematic through the use of highly sophisticated tools that block and filter internet content and monitor user activity. The majority of blocked websites feature critical news and opposition viewpoints run by individuals and organizations based mostly in the diaspora. Surveillance of mobile phone and internet networks is systematic and widespread, enabled by Chinese-made technology that allows for the interception of SMS text messages, recording of phone calls, and centralized monitoring of online activities. The government also employs commentators and trolls to proactively manipulate the online news and information landscape.
During the report’s coverage period, internet freedom in Ethiopia worsened due to increasing restrictions on access to social media and communications tools, such as Storify, and the temporary blocking of Facebook and Twitter in July 2013. A new law passed in November 2013 gave the Information Network Security Agency (INSA) carte blanche to track private online communications and investigate electronic devices without oversight. In addition, a number of diaspora journalists and exiled dissidents were targeted with surveillance malware, demonstrating a growing level of sophistication in the government’s effort to silence critical voices that extends beyond the country’s borders.
In 2014, the Ethiopian authorities increased their crackdown against bloggers and online journalists, using the country’s harsh laws to prosecute individuals for their online activities and quash dissent. Most alarmingly, six bloggers from the critical Zone9 blogging collective and three journalists associated with Zone9 were arrested in late April 2014 on charges of terrorism, which, under the Telecom Fraud Offenses Law and anti-terrorism proclamation, can entail a sentence of up to 20 years in prison if the bloggers are found guilty. The Zone9 case was repeatedly stalled by the courts throughout 2014, leaving the bloggers in pre-trial detention for over six months as of late-2014. Meanwhile, two online radio journalists were arrested and detained for a week without charges in August 2013, and the prominent dissident blogger, Eskinder Nega, and award-winning journalist, Reeyot Alemu, continue to serve lengthy prison sentences, despite international pressure for their release. The overall crackdown has had a major chilling effect on internet freedom and freedom of expression in the country, leading to increasing levels of self-censorship among online journalists, bloggers, and ordinary users alike.
Obstacles to Access
In 2013 and 2014, access to ICTs in Ethiopia remained extremely limited, hampered by slow speeds and the state’s tight grip on the telecom sector. According to the International Telecommunications Union (ITU), internet penetration stood at a mere 1.9 percent in 2013, up from 1.5 percent in 2012. Only 0.25 percent of the population had access to fixed-broadband internet, increasing from 0.01 percent in 2012.Ethiopians had more access to mobile phone services, with mobile phone penetration rates increasing from 22 percent in 2012 to 27 percent in 2013 though such access rates still lag behind a regional average of 80 percent. Meanwhile, less than 5 percent of the population has a mobile-broadband subscription. Radio remains the principal mass medium through which most Ethiopians stay informed. While access to the internet via mobile phones increased slightly in the last year, prohibitively expensive mobile data packages still posed a significant financial obstacle for the majority of the population in Ethiopia, where per capita income in 2013 stood at US$470.8 Ethiopia’s telecom market is very unsaturated due to monopolistic control, providing customers with few options at arbitrary prices. Prices are set by the state-controlled Ethio Telecom and kept artificially high. As of mid-2014, monthly packages cost between ETB 200 and 3,000 (US$10 to $150) for 1 to 30 GB of 3G mobile services.
The computer remains the most practical option for going online, though in 2014, personal computers are still prohibitively expensive. The combined cost of purchasing a computer, initiating an internet connection, and paying usage charges makes internet access beyond the reach of most Ethiopians. Consequently, only 2 percent of Ethiopian households had internet access in their homes in 2013. The majority of internet users rely on cybercafes to log online, leading to a growth of
cybercafes in recent years, particularly in large cities. A typical internet user in Addis Ababa pays between ETB 5 and 7 (US$0.25 to $0.35) for an hour of access. Because of the scarcity of internet cafes outside urban areas, however, rates in rural cybercafes are more expensive.
For the few Ethiopians who can access the internet, connection speeds are known to be painstakingly slow. For years, logging into an email account and opening a single message could take as long as six minutes at a standard cybercafe with broadband in the capital city.12 According to May 2014 data from Akamai’s “State of the Internet” report, Ethiopia has an average connection speed of 1.2 Mbps (compared to a global average of 3.9 Mbps). Meanwhile, Ethiopia’s broadband adoption (characterized by connection speeds greater than 4 Mbps) is less than 3 percent,14 while the country’s narrowband adoption (connection speed below 256 Kbps) is about 20 percent among those with access. Numerous users reported that internet and text messaging speeds were extremely slow during the coverage period, with services completely unavailable at times. Frequent electricity outages are also a contributing factor to poor telecom services. Despite reports of massive investments from Chinese telecom companies in recent years,17 Ethiopia’s telecommunications infrastructure is among the least developed in Africa and is almost entirely absent from rural areas, where about 85 percent of the population resides. The country is connected to the international internet via satellite, a fiber-optic cable that passes through Sudan and connects to its international gateway, and the SEACOM cable that connects through Djibouti to an international undersea cable. In an effort to expand connectivity, the government has reportedly installed several
thousand kilometers of fiber-optic cable throughout the country over the past few years. Construction of the East African Submarine Cable System (EASSy) was completed and launched in July 2010, but its effects on Ethiopia have yet to be seen as of mid-2014. The space for independent initiatives in the ICT sector, entrepreneurial or otherwise, is extremely
limited, with state-owned Ethio Telecom holding a firm monopoly over internet and mobile phone services in the country. Consequently, all connections to the international internet are completely centralized via Ethio Telecom, enabling the government to cut off the internet at will. As a result, the internet research company Renesys classified Ethiopia “as being at severe risk of Internet disconnection,” alongside Syria, Uzbekistan, and Yemen in a February 2014 assessment. During the coverage period, one Renesys report found that 40 percent of Ethiopia’s networks were down for a few hours on July 18, 2013 as a result of a disruption on the SEACOM network, though the exact reason for the disruption was unknown. In September 2013, a number of cybercafe owners in Ethiopia reported an increasing trend of unpredictable internet connections and speeds beginning in June that resulted in a significant decline in business, with internet connections reported as unavailable for up to 15 days in a month. Mobile phone networks—also completely centralized under Ethio Telecom—are similarly vulnerable to service disruptions and shutdowns by the government, which often occur during politically sensitive times. During the coverage period, there were frequent reports of dropped cell phone and landline calls, complete network blackouts in many parts of the country, and overlapping voices in calls. The latter phenomenon led people to suspect government engagement in a widespread eavesdropping scheme (see “Violations of User Rights” for details on surveillance). Meanwhile, cybercafes are subject to onerous requirements under the 2002 Telecommunications
(Amendment) Proclamation, which requires cybercafe owners to obtain an operating license with Ethio Telecom via a murky process that can take months. During the coverage period, Ethio Telecom began enforcing its licensing requirements more strictly in response to the increasing spread of cybercafes, reportedly penalizing Muslim cafe owners more harshly. Violations of the stringent requirements, such as a prohibition on providing Voice-over-IP (VoIP) services, entail criminal liability. Despite repeated international pressure to liberalize telecommunications in Ethiopia, the government
has not eased its grip on the sector. In June 2013, the prime minister publicly affirmed that the government would maintain a monopoly over the country’s telecoms. In the meantime, China has emerged as a key investor and contractor in Ethiopia’s telecommunications industry, and in July 2013, the government signed a US$1.6 billion agreement with the Chinese telecom companies,
Zhongxing Telecommunication Corporation (ZTE) and Huawei, to upgrade its broadband network to 4G in Addis Ababa and expand 3G across the country. The networks built by the Chinese firms have been criticized for their high costs and poor service, though the partnership has enabled Ethiopia’s authoritarian leaders to maintain their hold over the telecom sector. Furthermore, the contracts have led to increasing fears that the Chinese may also be assisting the authorities in developing more robust internet and mobile phone censorship and surveillance capacities.
The Ethiopian Broadcasting Authority (EBA) and the Ethiopian Telecommunications Agency (ETA) are the primary regulatory bodies overseeing the telecommunications sector. These two organizations were established as autonomous federal agencies, but both are highly controlled government bodies.
Limits on Content
During the coverage period, over a hundred websites remained inaccessible in Ethiopia, with a greater number of online tools and services targeted for blocking. A June 2014 report affirmed the government’s efforts to recruit and train progovernment citizens to attack politically objectionable content online.
The Ethiopian government imposes nationwide, politically motivated internet blocking and filtering that tends to tighten ahead of sensitive political events. The majority of blocked websites are those that feature opposition or critical content run by individuals or organizations based in the country or the diaspora. The government’s approach to internet filtering generally entails hindering access to a list of specific internet protocol (IP) addresses or domain names at the level of the Ethio Telecom-controlled international gateway. A more sophisticated strategy of blocking websites based on a keyword in the URL path, known as deep-packet inspection (DPI), was detected in May 2012 when the Tor network—an online tool that enables users to browse anonymously—was blocked. In January 2014, an independent test conducted by a researcher based in the country found 120 unique URLs that were inaccessible in the country, 62 of which were Ethiopian news websites, 14 of which were political party websites, of which were blogs, and 7 of which were television and online
radio websites. During the test, some websites opened at the first attempt but were inaccessible when refreshed. The test also found that select tools and services on Google’s Android operating system on smart phones were inaccessible at irregular intervals but for unclear reasons. A separate test on over 1,400 URLs between July and August 2013 by the OpenNet Initiative in partnership withHuman Rights Watch similarly found 62 websites blocked altogether and numerous others intermittently inaccessible. International news outlets were increasingly targeted for censorship. Al Arabiya, a Saudi Arabia-based media outlet, and both of Al Jazeera’s Arabic and English websites were intermittently blocked during the coverage period. In July 2013, websites belonging to Yahoo and CNN were reportedly inaccessible for about 12 hours. Facebook and Twitter were also targets of the short-term July 2013 blocking. There was no evident impetus or reason for the short-term blocking, and other major services such as Gmail and new outlets such as the New York Times remained accessible. Nevertheless, the incident further increased worries over reports of government plans to block popular social media tools completely. Facebook and Twitter platforms were otherwise generally accessible, although some individual Facebook groups belonging to opposition individuals remained blocked altogether, particularly when accessed via the unencrypted (http://) URL pathway. Meanwhile, the social media curation tool Storify—first blocked in July 201241—remained blocked during the coverage period, while the URL shortening tool Bit.ly was inexplicably blocked in late 2013.
In the past few years, the authorities have become more sophisticated in their censorship techniques, electing to block select webpages as opposed to entire websites. Critical online news articles are usually targeted, such as an August 2012 Forbes article titled, “Requiem for a Reprobate Ethiopian Tyrant Should Not Be Lionized,” which was blocked for criticizing the local and global praise of the former prime minister’s debatable economic growth achievements; the article remained blocked as of June 2014.44 A July 2013 YouTube video of the anti government Muslim protests that occurred from 2012-13 was also blocked as of late 2013.
International blog-hosting platforms such as Blogspot have been frequently blocked since the disputed parliamentary elections of 2005, during which the opposition used online communication tools to organize and disseminate information that was critical of the ruling Ethiopian People’s Revolutionary Democratic Front. In 2007, the government instituted a blanket block on the domainnames of two popular blog-hosting websites, Blogspot and Nazret, though the authorities have
since become more sophisticated in their censorship techniques, now blocking select pages such as the Zone9 independent blog hosted on Blogspot, as opposed to the entire blogging platform. Nazret, however, remained completely blocked as of June 2014. Circumvention strategies have also been targeted, with the term “proxy” yielding no search results on Google, according to an independent source. Meanwhile, the terms “sex” or “porn” are still searchable.
In addition to increasing blocks of online content, politically objectionable content is often targeted for removal, often by way of threats from security officials who personally seek out users and bloggers to instruct them to take down certain content, particularly critical content on Facebook. The growing practice suggests that at least some voices within Ethiopia’s small online community are being closely monitored. Some restrictions are also placed on mobile phones, such as the requirement for a text message to obtain prior approval from Ethio Telecom if it is to be sent to more than ten recipients. A bulk text message sent without prior approval is automatically blocked. There are no procedures for determining which websites are blocked or why, which precludes any avenues for appeal. There are no published lists of blocked websites or publicly available criteria for how such decisions are made, and users are met with an error message when trying to access
blocked content. This lack of transparency is exacerbated by the government’s continued denial of its censorship efforts. Meanwhile, the decision-making process does not appear to be controlled by a single entity, as various government bodies—including the Information Network Security Agency (INSA), Ethio Telecom, and the ministry of ICT—seem to be implementing their own lists, contributing to a phenomenon of inconsistent blocking. Lack of adequate funding is a significant challenge for independent online media in Ethiopia, as fear of government pressure dissuades local businesses from advertising with politically critical websites. Local newspapers and web outlets receive their news and information from regime critics and opposition organizations in the diaspora. While the domestic Ethiopian blogosphere has been expanding, most blogging activity on Ethiopian issues still originates in the diaspora. Few Ethiopian journalists work for both the domestic print media and overseas online outlets due to the threat of repercussions. Increasing repression against journalists and bloggers has had a major chilling effect on expression online, particularly following the arrest of the Zone9 bloggers in April 2014 (see “Violations of User Rights”). Fear of pervasive surveillance has led to widespread self-censorship, and many bloggers publish anonymously to avoid reprisals. Notably, users on social media platforms such as Facebook and Twitter seem to practice a lower degree of self-censorship, which may be due to poor awareness of privacy settings, or the perception that posts on social media are anonymous or more secure. Despite extremely low levels of internet access, the authorities employ progovernment commentators and trolls to proactively manipulate the online news and information landscape. Acrimonious exchanges between commentators on apologist websites and an array of diaspora critics and opposition figures have become common in online political debates. There was a noticeable increase in the number of progovernment commentators during the coverage period, as confirmed in a June 2014 report by the Ethiopian Satellite Television Service (ESAT) that detailed the government’s efforts to recruit and train progovernment citizens to attack politically objectionable content online. According to the ESAT report, hundreds of bloggers who report directly to government officials had been trained on how to post progovernment comments and criticize antigovernment articles on social media platforms. As the country prepares for the upcoming 2015 National Election, the state media has stepped up its campaign against the press in general and the use of social media in particular, claiming that foreign agents and terrorists are using social media to destabilize the country. Consequently, many civil society groups based in the country are wary of mobilizing against the government, and calls for protest come mostly from the Ethiopian diaspora rather than from local activists who fear the government’s violent crackdowns against protest movements. Nevertheless, over the past few years, Facebook has become one of the most popular mediums through which Ethiopians share and consume information. Social media services have also become significant platforms for political deliberation and social justice campaigns. For example, in September 2013, a group of young Ethiopian bloggers and activists based in Addis Ababa launched a Facebook and Twitter campaign on the occasion of Ethiopia’s New Year celebration to share their vision of a better Ethiopia, using the hashtag #EthiopianDream.52 In November 2013, Ethiopians responded to the Saudi government’s crackdown on undocumented Ethiopian immigrants in Saudi Arabia by organizing the online campaign, #SomeoneTellSaudiArabia, to protest the abusive treatment of Ethiopian immigrants. Netizen activism was particularly pronounced and widespread following the arrest of six Zone9 bloggers and three journalists for their alleged affiliation with the Zone9 collective (see “Violations of User Rights”). Ethiopian bloggers and social media users flocked online to spread the #FreeZone-9Bloggers hashtag in a campaign that quickly swept across the social media sphere and garnered
widespread support from around the world. Within five days, the #FreeZone9Bloggers hashtag had been tweeted more than 8,000 times. Unfortunately, the international campaign elicited no response from the government, and the imprisoned bloggers and journalists are still awaiting trial on charges of terrorism as of late-2014.
Violations of User Rights
During the coverage period, the Ethiopian government’s already limited space for online expression continued to deteriorate alongside its poor treatment of journalists. A new proclamation passed in November 2013 empowered INSA with sweeping surveillance capabilities without judicial oversight. Sophisticated malware was launched against online radio journalists and dissidents in exile, while repression against bloggers and ICT users in the country increased notably. Six bloggers of the critical Zone9 blogging collective were arrested for their alleged terrorist activities. The 1995 Ethiopian constitution guarantees freedom of expression, freedom of the press, and access to information, while also prohibiting censorship. These constitutional guarantees are affirmed in the 2008 Mass Media and Freedom of Information Proclamation, known as the press law, which also provides certain protections for media workers, such as prohibiting the pre-trial detention of journalists. Nevertheless, the press law also includes problematic provisions that contradict constitutional protections and restrict free expression. For example, media outlets are required to obtain licenses to operate through an onerous registration process that applies to all outlets, regardless of size, though it is uncertain whether the press law’s broad language encompasses online media. Penalties for violating the registration requirement and other restrictions on content, such as defamation, involve high fines and up to two and three years in prison, respectively.
In September 2012, the government codified specific restrictions on various telecommunications activities through the passage of the Telecom Fraud Offences law, which revised a 1996 law that had placed bans on certain communication applications, such as Voice over Internet Protocol (VoIP)60— including Skype and Google Voice—call back services, and internet-based fax services. Under the new law, the penalties under the preexisting ban were toughened, increasing the fine and maximum prison sentence from five to eight years for offending service providers, and penalizing users with
three months to two years in prison. The law also added the requirement for all individuals to register their telecommunications equipment—including smart phones—with the government, which security officials typically enforce by confiscating ICT equipment when a registration permit cannot be furnished at security checkpoints, according to sources in the country.
Most alarmingly, the Telecom Fraud Offences law extended the violations and penalties defined in the 2009 Anti-Terrorism Proclamation and 2004 Criminal Code to electronic communications, which are broadly defined yet explicitly include both mobile phone and internet services. The anti-terrorism legislation prescribes prison sentences of up to 20 years for the publication of statements that can be understood as a direct or indirect encouragement of terrorism, vaguely defined.64 Meanwhile, the criminal code holds any “author, originator or publisher” criminally liable for content allegedly linked to offenses such as treason, espionage, or incitement, which carries with it the penalty of up to life imprisonment or death. The criminal code also penalizes the publication of a “false rumor” with up to three years in prison. In 2014, the Ethiopian authorities increased their crackdown against bloggers and online journalists, using the country’s harsh laws to prosecute individuals for their online activities and silence dissent. Most alarmingly, six bloggers from the critical Zone9 blogging collective and three journalists associated with Zone9 were arrested in late April 2014 on charges of terrorism. They were accused of “working with foreign organizations that claim to be human rights activists… and receiving finance to
incite public violence through social media,” though the arrests had occurred just days following Zone9’s Facebook post announcing plans to resume its activism. The blogging collective had been inactive for seven months as a result of “a considerable amount of surveillance and harassment” the bloggers had suffered at the hands of security agents for their writings and social media activism. Despite widespread international condemnation of the Zone9 arrests, the detainees were denied bail in August and remained in jail as of fall 2014, awaiting trial. Meanwhile, the well-known dissident journalist and blogger Eskinder Nega is still carrying out an 18-year prison sentence handed down in July 2012 under the anti-terrorism law. Numerous other journalists and media outlets—both online and print—were targeted for arrest and prosecutions during the coverage period, including Darsema Sori and Khalid Mohammed who were arrested in August 2013 for their work with the online radio station, Radio Bilal, which is known for its extensive coverage of the 2012-13 anti government protests organized by Ethiopian Muslims.
They were released after being held for a week without charges,71 but the arrests were in keeping with the government’s concerted efforts to silence the protests. Given the high degree of online repression in Ethiopia, some political commentators use proxy servers and anonymizing tools to hide their identities when publishing online and to circumvent filtering, though the ability to communicate anonymously has become more difficult. The Tor Network anonymizing tool was blocked in May 2012, confirming that the government has deployed deep-packet inspection technology, and Google searches of the term “proxy” mysteriously yield no results. Anonymity is further compromised by strict SIM card registration requirements. Upon purchase of a SIM card through Ethio Telecom or an authorized reseller, individuals must provide their full name, address, government-issued identification number, and a passport-sized photograph. Ethio Telecom’s database of SIM registrants enables the government to cut-off the SIM cards belonging to targeted individuals and to restrict those individuals from registering for new SIM cards. Internet subscribers are also required to register their personal details, including their home address, with the government. In 2013, an inside informant leaked worrying details of potential draft legislation that seeks to mandate real-name registration for all internet users in Ethiopia, though there are no further
details of this development as of mid-2014. Government surveillance of online and mobile phone communications is pervasive in Ethiopia, and evidence has emerged in recent years that reveal the scale of such practices. According to 2014
Human Rights Watch research, there are strong indications that the government has deployed a centralized monitoring system from the Chinese telecommunications firm ZTE, known as ZXMT, to monitor phone lines and various types of communications, including mobile phone networks and the internet.73 Known for its use by repressive regimes in Libya and Iran, ZXMT enables deep-packet inspection (DPI) of internet traffic across the Ethio Telecom network and has the ability to intercept emails and web chats. Another ZTE technology, known as ZSmart, is a customer management database installed at Ethio Telecom that provides the government with full access to user information and the ability to intercept SMS text messages and record phone conversations. ZSmart also allows security officials to locate targeted individuals through real-time geolocation tracking of mobile phones. While the extent to which the government has made use of the full range of ZTE’s sophisticated surveillance systems is unclear, the authorities frequently present intercepted emails and phone calls as evidence during trials against journalists and bloggers or during interrogations as a scare tactic. In November 2013, a new Cyber Security Law expanded the surveillance powers of the Information Network Security Agency (INSA)—the government body established in 2011 to preside overcurity of the country’s critical communications infrastructure. According to reports, the law states that “social media outlets, blogs and other internet related media have great capabilities to instigate war, to damage the country’s image and create havoc in the economic atmosphere of the country”—
setting the logic for expanding INSA’s duties to include developing offensive cyber capabilities and ICT tools. The proclamation also empowers INSA to investigate computers, networks, internet, radio, television, and social media platforms “for any possible damage to the country’s social, economic, political and psychological well being.” INSA reportedly uses sophisticated spyware, such as the commercial toolkit FinFisher—a device that can secretly monitor computers by turning on webcams, record everything a user types with a key logger, and intercept Skype calls—to target dissidents and supposed threats. A leaked document confirmed that the UK-based company, Gamma International, had provided Ethio Telecom with the FinFisher surveillance toolkit at some point between April and July 2012.80 In addition, research conducted by Citizen Lab in March 2013 worryingly found evidence of an Ethio Telecom-initiated inSpy campaign launched against users that employed pictures of the exiled prodemocracy group, Ginbot 7, as bait. There has been an increasing trend of exiled dissidents targeted with surveillance malware in the past few years. In April 2013, Tadesse Kersmo, a senior member of Ginbot-7 living in exile in the United Kingdom since 2009, came across the above-mentioned Citizen Lab FinSpy report and noticed that one of the spyware campaign’s bait was a picture of himself. He contacted Citizen Lab to have his computer examined and found that FinSpy had been active on his computer over two days in June 2012. The spyware may have transmitted any or all of Kersmo’s emails, chats, Skype calls, files, and web searches to a server based in Ethiopia, which could have provided the authorities with names of contacts, colleagues, and family members still living in the country. In February 2014, Privacy International filed a criminal complaint to the UK’s National Cyber Crime Unit on Kersmo’s behalf, urging them to investigate the potential unlawful interception of communications.
In the same month, the Electronic Frontier Foundation filed a similar suit in the United States on behalf of another Ethiopian dissident (and American citizen) identified publicly under the pseudonym Mr. Kidane. Kidane’s computer had also been found infected with the FinSpy malware sometime between late October 2012 and March 2013, which had secretly recorded dozens of his Skype calls, copied emails he had sent, and logged a web search conducted by his son on the history of sports medicine for a school research project.86 The FinSpy IP address was linked to a server belonging to
Ethio Telecom. Recent Citizen Lab research published in February 2014 uncovered the use of Remote Control System
(RCS) spyware against two employees of the diaspora-run independent satellite television, radio, and online news media outlet, Ethiopian Satellite Television Service (ESAT), based in Alexandria, VA.87 Made by the Italian company Hacking Team, RCS spyware is advertised as “offensive technology” sold exclusively to law enforcement and intelligence agencies around the world, and has the ability to steal files and passwords, and intercept Skype calls/chats. 88 While Hacking Team claims that they do not deal with “repressive regimes,” the RCS virus sent via sophisticated bait to the two ESAT employees made it clear that the attack was targeted, and researchers have strong suspicions of the Ethiopian government’s involvement.
While the government’s stronghold over the Ethiopian ICT sector enables it to proactively monitor users, its access to user activity and information is less direct at cybercafes. For a period following the 2005 elections, cybercafe owners were required to keep a register of their clients, but the requirement has not been enforced since mid-2010.91 Nevertheless, some cybercafe operators revealed that they are required to report any “unusual behavior” to security officials, and officials often visit cybercafes (sometimes in plainclothes) to ask questions about specific users or monitor user activity themselves.
Government security agents frequently harass and intimidate bloggers, online journalists, and ordinary users for their online activities. Independent bloggers are often summoned by the authorities to be warned against discussing certain topics online, while activists claim that they are consistently threatened by state security agents for their online activism. Bloggers from Zone9, for example, reported suffering a considerable amount of harassment for their work, leading them to go silent for several months. Shortly after the blog announced on Facebook that it was resuming activities in April 2014, six Zone9 bloggers were arrested and sent to a federal detention center in Addis Ababa where the torture of detainees is reportedly common. The active Gmail accounts belonging to several of the Zone9 bloggers94 while in detention suggests that they may have been forced give their passwords to security officials against their will.
Read more @ https://freedomhouse.org/sites/default/files/FOTN_2014_Full_Report_compressedv2_0.pdf
ETHIOPIA: ‘BECAUSE I AM OROMO’: SWEEPING REPRESSION IN THE OROMIA REGION OF ETHIOPIA
http://www.amnesty.org/en/library/info/AFR25/006/2014/en
 (New York, August 13, 2015) – The Italian spyware firm Hacking Team took no effective action to investigate or stop reported abuses of its technology by the Ethiopian government against dissidents, Human Rights Watch said. A comprehensive review of internal company emails leaked in July 2015 reveals that the company continued to train Ethiopian intelligence agents to hack into computers and negotiated additional contracts despite multiple reports that its services were being used to repress government critics and other independent voices.
(New York, August 13, 2015) – The Italian spyware firm Hacking Team took no effective action to investigate or stop reported abuses of its technology by the Ethiopian government against dissidents, Human Rights Watch said. A comprehensive review of internal company emails leaked in July 2015 reveals that the company continued to train Ethiopian intelligence agents to hack into computers and negotiated additional contracts despite multiple reports that its services were being used to repress government critics and other independent voices.









 25 March 2015 (Privacy International) — German surveillance technology company
25 March 2015 (Privacy International) — German surveillance technology company 




You must be logged in to post a comment.